OA Product Security Incident Response Team

We acknowledge the importance for our customers to rely on secure products and solutions. Therefore it is our goal to ensure that On Access(OA) products are developed with all appropriate security principles as basis. We follow a comprehensive security program that combines:
- Secure software development best practices, processes, and tools
- Rigorous product security requirements
- Periodic validation and quality of security testing before release
Despite these security principles and related actions, vulnerabilities can be discovered in the software components of our products which, when exploited, can have an impact on the security level of these products once deployed in customer's networks.
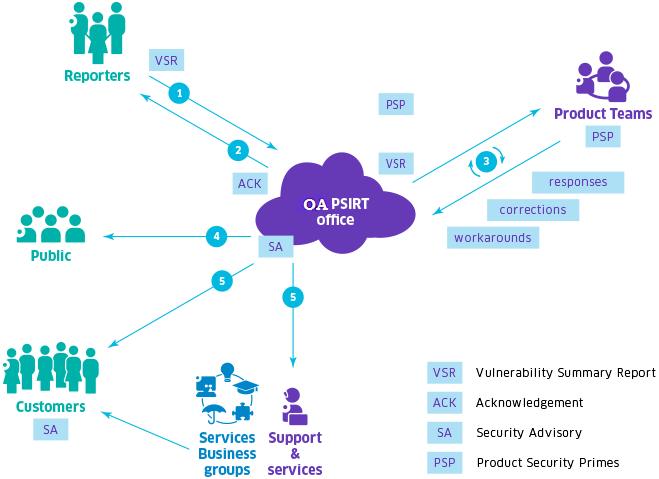
Addressing security issues is the responsibility of the OA Product Security Incident Response Team (PSIRT). OA PSIRT is dedicated to manage the requests, investigation and reporting about vulnerabilities or technical issues impacting OA products and solutions.
Reporting a suspected Security Vulnerability
Individuals or organizations that are experiencing technical security issue with an OA product or solution are strongly encouraged to contact the OA PSIRT by following these steps:
- Obtain the OA PSIRT PGP public key, this will ensure the confidentiality of the communication. Confidentiality is a key point at this step to protect the security of our customers in regards with our responsible disclosure policy.
- Complete the vulnerability summary report (VSR)
- Consider sending the report email with the reporting organization’s public PGP key and by encrypting the message with the OA PSIRT PGP public key.
The OA PSIRT process detailed here under will be followed while maintaining the discussion with the reporter. Communication with all involved parties is a key activity in our vulnerability solution process.
Other channels for contacting On Access
Customers are also encouraged to report suspected security vulnerabilities via their usual support channels.
Depending on the maintenance contract, these contact points will be able to assist in more general situations such as:
- technical assistance to determine if a security problem exists
- configuring an OA product for a specific security-related function
- questions about an announced security problem with an OA product
- Implementation of any workarounds defined for the vulnerability
Note that OA PSIRT should NOT be contacted to report or get support for security incidents that are happening "live" in deployed networks and solutions. Such incidents are to be reported only via the usual customer support channels.
OA Product Security Incident Response Process
- OA acknowledges the reception of the VSR to the reporter
- OA PSIRT analyzes the relevancy. Reporters will be informed on a regular basis about the status information of ongoing investigation of the vulnerability
- OA PSIRT communicates analysis conclusions with the reporter
- If any impacts are confirmed OA will:
- Coordinate fix and impact assessment
- Define timeframe of correction delivery, notification plans, and disclosure to public organizations such as mitre.org and CERT organizations
Confidentiality - OA PSIRT PGP public key
OA PSIRT process ensures that neither unauthorized OA employees nor outside users will get access to the information provided by the incident reporter. OA also guarantees that on request, the name of the incident reporter will not be disclosed in public communications or be used in further external distribution. Similarly, the OA PSIRT asks incident reporters to maintain strict confidentiality until complete resolutions are available for customers and have been published by the OA PSIRT on the OA websites through the appropriate coordinated disclosure.
For ensuring the confidentiality of the reporting and following steps of communication with OA PSIRT, we encourage sending encrypted messages using the following OA PGP public key and sending in return the public PGP key of the incident reporter.
Third-Party Software Vulnerabilities
OA PSIRT works with third-party coordination centers such as CERT-IST, NVD, US-CERT to manage vulnerabilities notices reported on third-party software embedded or used in OA products and solutions. The reports are referred to with a unique CVE number (Common Vulnerabilities and Exposures After). Each issued CVE is analyzed by OA teams to provide an adjusted risk score that reflect s the effective impact on our products.
Risk assessment
OA PSIRT uses the version 3.0 of the Common Vulnerability Scoring System (CVSS) for evaluation of the reported and analyzed vulnerabilities. Although the cvss numerical score gives standard information about the estimated risk on a given vulnerability, we often abstract it to a more comprehensive scale of impact with following values:
|
Risk impact |
CVSS score |
Color code |
|
Critical |
9.0–10.0 |
|
|
High |
7.0–8.9 |
|
|
Medium |
4.0–6.9 |
|
|
Low |
3.9 or below |
|
Responsible Disclosure
If one or more of the following conditions exist, OA will publicly disclose a Security Advisory:
- An incident response process has been completed and it has been determined that enough software patches or workarounds exist to address the vulnerability, or subsequent public disclosure of code fixes is planned to address high to critical severity vulnerabilities
- An active exploitation of vulnerability has been observed that could lead to increased risk for our customers. Early Security Advisories may then be published prior to the publication of available patches or corrections in order to inform our customers about potential risks.
- Public information about the vulnerability can expose our customers to potential increased risk. Early Security Advisories may then be published prior to the publication of available patches or corrections in order to inform our customers about potential risks.
All security publications are disclosed via the OA business portal website. OA reserves the right to deviate from this policy on an exception basis to ensure software patch availability and our customer’s security.